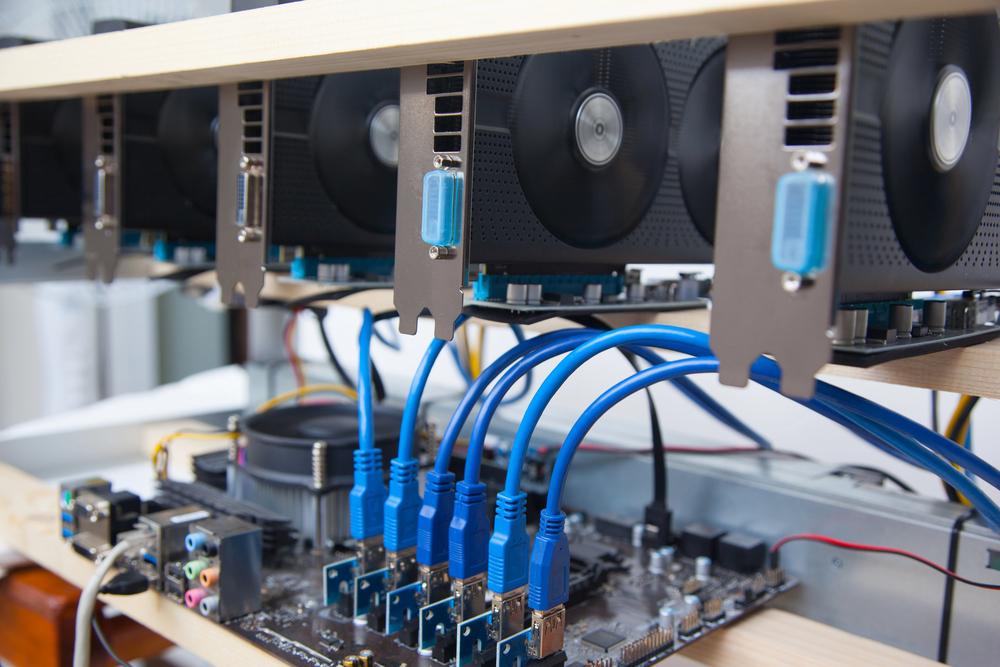
In today’s digital age, where cryptocurrencies have gained significant popularity, mining rigs have become valuable assets. However, they are also attractive targets for hackers who exploit vulnerabilities and steal valuable resources. As a responsible miner, protecting your mining rig from potential threats is essential. This comprehensive guide will provide valuable insights and practical steps to fortify your mining rig’s security and keep your hard-earned rewards safe.
Understand the Risks Associated with Mining Rigs:
Before diving into protective measures, it’s crucial to comprehend the potential risks your mining rig faces. Hackers can exploit vulnerabilities through various avenues, such as:
-
- a) Malware Attacks: Malicious software can infect your mining rig, leading to unauthorized access and control.
- b) Network Intrusions: Hackers can exploit weak network security protocols to gain entry into your mining rig and compromise its operations.
- c) Physical Security Breaches: Intruders may attempt to physically tamper with your mining rig to gain unauthorized access or manipulate its components.
Update Your Mining Rig’s Software Regularly:
Keeping your mining rig’s software up to date is an effective way to enhance its security. Manufacturers often release updates that address potential vulnerabilities and improve system performance. By promptly installing these updates, you ensure that your rig has the latest security patches, reducing the risk of exploitation.
Implement Robust Password Management:
Strong passwords are the first line of defense against unauthorized access. Create unique and complex passwords for all accounts associated with your mining rig, including the operating system, mining software, and wallet applications. Utilize a reliable password manager to securely store and manage these passwords, ensuring they are not easily guessable.
Utilize Two-Factor Authentication (2FA):
Implementing 2FA adds an extra layer of security to your mining rig. By enabling this feature, you ensure that only authorized individuals with the correct password and a secondary authentication factor, such as a unique code generated on your mobile device, can access your rig. This mitigates the risk of unauthorized access even if your password gets compromised.
Secure Your Network:
Protecting your mining rig’s network is crucial to prevent unauthorized access and data breaches. Consider the following steps:
-
- a) Router Security: Change the default credentials of your router and enable robust encryption protocols (e.g., WPA2 or WPA3) to secure your Wi-Fi network.
- b) Firewall Configuration: Enable firewalls on your router and mining rig to filter incoming and outgoing traffic, blocking potential threats.
- c) Guest Network Isolation: Create a separate guest network for visitors, keeping them isolated from your mining rig’s network and minimizing potential vulnerabilities.
Install Reliable Antivirus and Anti-Malware Software:
Deploying reputable antivirus and anti-malware software adds layer of protection against malicious programs. Regularly scan your mining rig for potential threats, and ensure your security software is up to date to combat emerging risks effectively.
Regularly Backup Your Data:
Perform regular backups of your mining rig’s data to mitigate the risk of data loss or corruption caused by hacking attempts or hardware failures. Store the backups securely offline or in a cloud storage service with robust encryption and access controls.
Employ Physical Security Measures:
Physical security is often overlooked but is crucial in safeguarding your mining rig. Consider the following measures:
- Secure Location: Keep your mining rig in a physically secure location, such as a locked room or cabinet, away from prying eyes.
- Tamper-Evident Seals: Utilize tamper-evident seals on the case of your mining rig to detect any unauthorized access attempts.
- Surveillance Cameras:
-
- Employ Physical Security Measures:
- Secure Location: Keep your mining rig in a physically secure location, such as a locked room or cabinet, away from prying eyes.
- Tamper-Evident Seals: Utilize tamper-evident seals in the case of your mining rig to detect any unauthorized access attempts.
- Surveillance Cameras: Install cameras near your mining rig to monitor and deter potential intruders.
- Alarm Systems: Consider installing an alarm system that triggers an alert in case of unauthorized access or tampering with your rig.
- Employ Physical Security Measures:
Educate Yourself on Social Engineering Attacks:
Hackers often employ social engineering techniques to manipulate individuals and gain unauthorized access to their systems. Stay vigilant and educate yourself on common social engineering tactics like phishing emails, fake websites, or phone calls impersonating technical support. Be cautious when sharing sensitive information, and always verify the legitimacy of requests before taking action.
Regularly Monitor Your Mining Rig:
Stay proactive by monitoring your mining rig’s performance and behavior. Regularly review logs and mining pool statistics to identify any irregularities that may indicate a security breach. Watch for suspicious activities, unexpected changes in hash rates, or sudden system slowdowns.
Conclusion:
Protecting your mining rig from hackers is essential to safeguard your investments and hard-earned rewards. By following the security measures outlined in this guide, including updating software, implementing solid passwords and 2FA, securing your network, installing reliable security software, backing up data, and employing physical security measures, you can significantly reduce the risk of unauthorized access and exploitation.
Remember, maintaining a strong security posture requires ongoing effort and staying up to date with emerging threats. By prioritizing the protection of your mining rig, you can mine cryptocurrencies with peace of mind and focus on maximizing your profits in a secure environment. Stay proactive, stay informed, and keep your mining rig safe from potential hackers.