In the dynamic and ever-evolving landscape of cryptocurrency, a grasp of the underlying technology is not just beneficial—it’s absolutely essential. At the core of this complex digital universe lies a fundamental component known as SHA-256, which has played a pivotal role in the security and functionality of cryptocurrencies like Bitcoin. Whether you’re a seasoned crypto miner navigating the intricacies of blockchain or someone who’s merely curious about the world of digital currencies, this guide aims to unravel the mysteries of SHA-256, shedding light on its profound significance in fortifying the realm of cryptocurrencies, including Bitcoin.
What is SHA-256?
SHA-256, an acronym for Secure Hash Algorithm 256-bit, may initially strike you as a formidable technical jargon. However, let’s strip away the complexity and break it down into more digestible terms.
Breaking it Down: Secure Hash Algorithm
Imagine a hash function as a digital fingerprint generator. Its primary function is to take any input, whether it’s a piece of data or a simple message, and transform it into a fixed-length string of characters. This string, referred to as the hash value or digest, serves as a unique identifier for each distinct input. Remarkably, even the tiniest alteration in the input data yields an entirely different hash value.
The term ‘Secure’ in SHA-256 underscores its remarkable resistance to reverse engineering. In simpler words, deciphering the original input data by inspecting the hash value alone is a Herculean task. This inherent property plays a pivotal role in safeguarding cryptocurrencies like Bitcoin against malicious intrusions and data breaches.
The Mighty 256-bit
The ‘256-bit’ component signifies the length of the hash value generated by SHA-256. In the realm of cryptography, longer hash values are often perceived as more robust and secure. SHA-256, as a 256-bit hash function, produces a hash value consisting of 64 characters. This lengthy string of characters translates into an astronomical number of potential combinations, rendering it exceedingly resistant to brute-force attacks and unauthorized access.
Why is SHA-256 Crucial in the Cryptocurrency Universe, Including Bitcoin?
Now that we’ve demystified this technical term, let’s delve into the critical role that SHA-256 plays in ensuring the security of cryptocurrencies like Bitcoin.
Facilitating Secure Transactions
Whenever you engage in cryptocurrency transactions, whether it involves sending or receiving digital assets like Bitcoin, SHA-256 comes into play. The details of the transaction, including the sender’s wallet address, the recipient’s wallet address, and the transaction amount, are all subjected to the SHA-256 hashing process. This resulting hash value serves as the digital signature of the Bitcoin transaction, guaranteeing its integrity and authenticity.
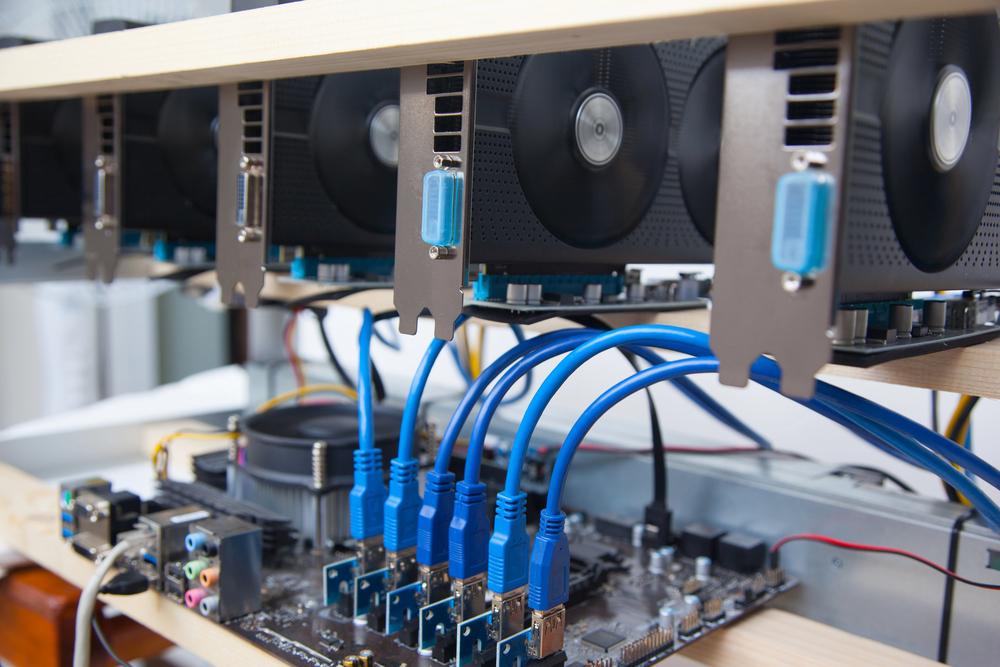
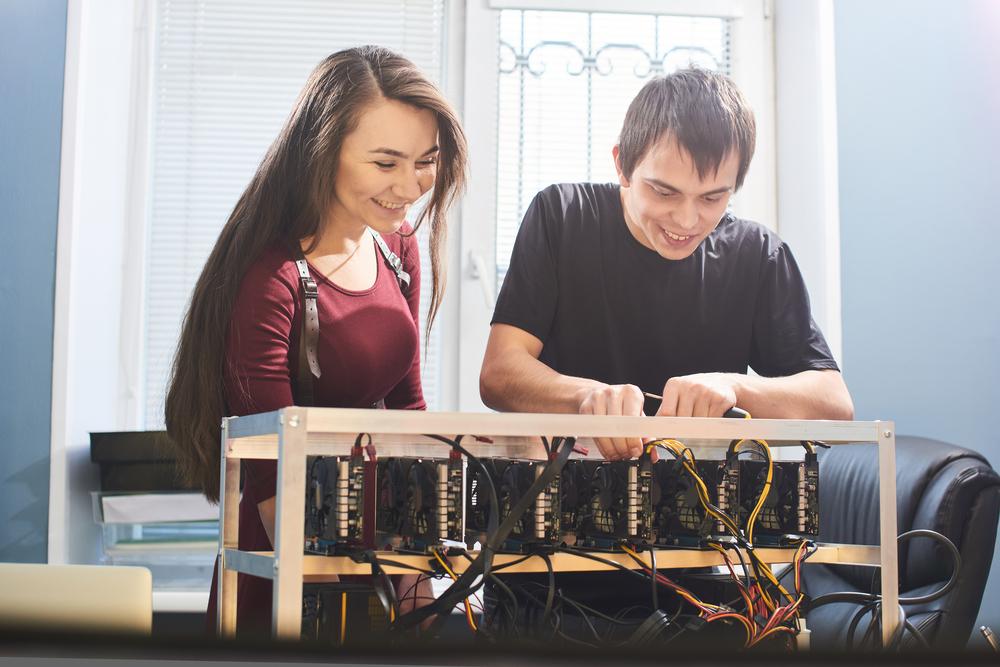
Powering Cryptocurrency Mining and Proof of Work (PoW), Especially in Bitcoin
Cryptocurrency mining, particularly in the context of Bitcoin, heavily relies on SHA-256. Miners engage in a competitive race to solve intricate mathematical puzzles, with the first miner to solve it earning the privilege to add a new block to the Bitcoin blockchain. SHA-256 lies at the heart of these complex puzzles, ensuring fairness and security within the Bitcoin network.
Safeguarding the Immutable Blockchain, Including Bitcoin’s
The blockchain, the decentralized ledger that meticulously records all cryptocurrency transactions, depends on SHA-256 to maintain its immutability. Once a block is seamlessly added to the blockchain, any attempt to alter its data would necessitate a change in the block’s hash value. Thanks to SHA-256’s resistance to tampering, the Bitcoin blockchain remains steadfastly secure and transparent, bolstering trust in the digital currency ecosystem.
In conclusion, SHA-256 emerges as the unsung hero of the cryptocurrency domain, toiling tirelessly in the background to fortify the security and authenticity of every digital coin transaction, including those involving Bitcoin. As you journey deeper into the world of cryptocurrency mining on ResidentialMiner.com, remember that a firm grasp of SHA-256 is your initial stride towards becoming a savvy and security-conscious miner, especially in the context of Bitcoin and similar cryptocurrencies.
Here’s what crypto miners need to know about SHA-256:
- Foundation of Security: SHA-256, or Secure Hash Algorithm 256-bit, is the cornerstone of security in cryptocurrency networks. Miners should be aware that it’s the algorithm responsible for securing transactions and maintaining the integrity of the blockchain.
- Hashing for Validation: SHA-256 is used to hash transaction data. Miners must comprehend that when they mine a new block, they’re essentially solving complex mathematical puzzles by applying SHA-256 to the block’s data. This process validates and secures transactions within the blockchain.
- Proof of Work (PoW): Cryptocurrencies like Bitcoin use PoW as their consensus mechanism. Miners compete to solve PoW puzzles, and SHA-256 is the driving force behind these puzzles. Understanding how SHA-256 fits into PoW is crucial for miners aiming to participate effectively.
- Difficulty Adjustment: Miners should be aware that the difficulty of mining new blocks in many cryptocurrencies, including Bitcoin, adjusts regularly. SHA-256 plays a role in determining this difficulty level, making it essential for miners to adapt their mining strategies accordingly.
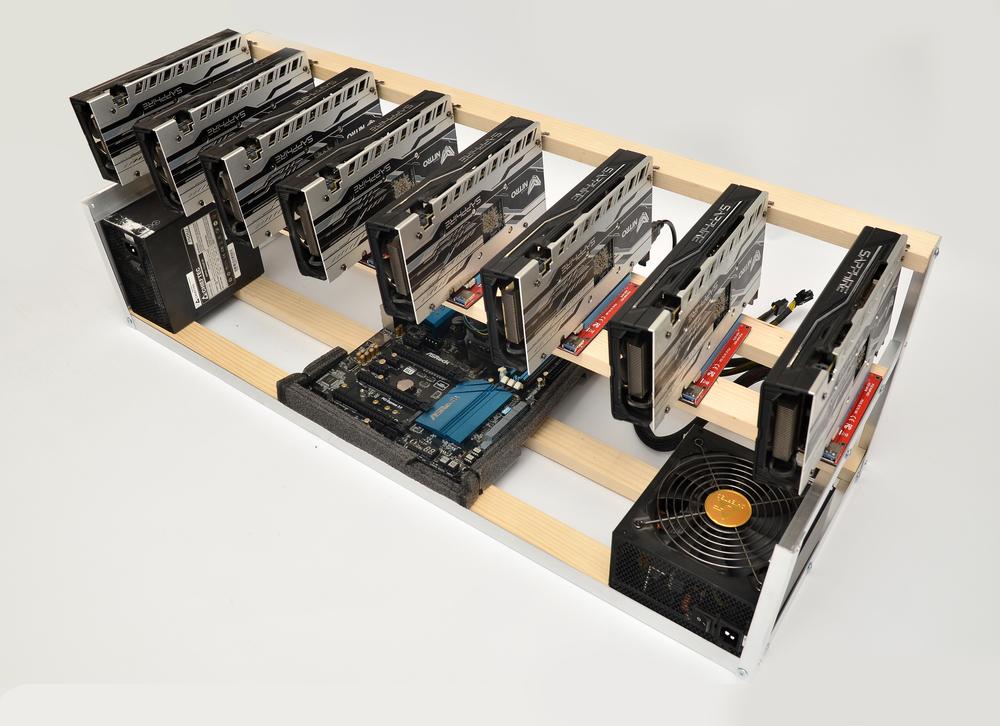
- Hash Rate: SHA-256’s efficiency is often measured in hash rate, which indicates how quickly a miner’s hardware can perform the hashing required for mining. Miners need to consider hash rate when selecting their equipment and optimizing their mining operations.
- Hardware Compatibility: Different cryptocurrencies may use variations of SHA-256 or entirely different hashing algorithms. Miners need to ensure that their mining hardware is compatible with the specific algorithm used by the cryptocurrency they intend to mine.
- Security Best Practices: Understanding SHA-256’s resistance to reverse engineering is vital for miners. It reinforces the importance of keeping private keys secure and following best practices for wallet management.
- Energy Efficiency: As the cryptocurrency mining landscape evolves, miners need to consider the energy efficiency of their mining operations. SHA-256 mining can be energy-intensive, so miners must weigh the costs and environmental impact.
- Network Consensus: Miners are part of a decentralized network, and SHA-256 is what ensures consensus among network participants. Miners must comprehend how their mining activities contribute to the overall security and decentralization of the network.
- Algorithm Evolution: Cryptography is a dynamic field, and while SHA-256 has proven its security, miners should stay informed about any developments or potential advancements in hashing algorithms that could impact the security of their chosen cryptocurrency.
In summary, SHA-256 is the cryptographic engine that powers the security and consensus of many cryptocurrencies, including Bitcoin. Crypto miners must grasp its role in hashing transaction data, securing the blockchain, and contributing to the PoW process. This knowledge is essential for making informed decisions regarding hardware, energy efficiency, and overall mining strategy. By understanding SHA-256, miners can navigate the complex world of cryptocurrency mining with confidence and effectiveness.













1 Comment
Cryptocurrency scams and hacks